Prevent XSS “on” Attribute Attacks in CKEditor 3.x
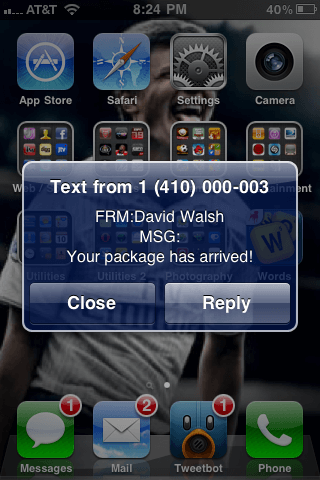
CKEditor 3.x had issues with XSS /security issues with on attributes. For example, you could trigger malicious code via an onerror attribute -- ouch! Of course the problem has been fixed in CKEditor 4 but upgrading can be an issue if you have custom plugins. Here's how the issue can be solved!
The JavaScript
We'll use prototype monkey-patching to accomplish this security fix:
// Prevent bad on* attributes (https://github.com/ckeditor/ckeditor-dev/commit/1b9a322)
var oldHtmlDataProcessorProto = CKEDITOR.htmlDataProcessor.prototype.toHtml;
CKEDITOR.htmlDataProcessor.prototype.toHtml = function(data, fixForBody) {
function protectInsecureAttributes(html) {
return html.replace( /([^a-z0-9<\-])(on\w{3,})(?!>)/gi, '$1data-cke-' + CKEDITOR.rnd + '-$2' );
}
data = protectInsecureAttributes(data);
data = oldHtmlDataProcessorProto.apply(this, arguments);
data = data.replace( new RegExp( 'data-cke-' + CKEDITOR.rnd + '-', 'ig' ), '' );
return data;
};
The toHtml method of CKEDITOR.htmlDataProcessor is modified to remove the troublesome on attributes during HTML render within the editor, but the attributes are indeed kept within the editor contents value and will display when you switch CKEditor to source mode. Problem solved!



I also noticed that, so what next ????